This content is viewable by Everyone
UC Celebrates CSAM 2021
More information and events added every day so please check back!
The National Cyber Security Alliance created Cyber Security Awareness Month (CSAM) to promote resources to help everyone to stay safe and secure online. UC is a proud sponsor and many of the UC campuses will be providing resources and holding events to help meet this objective.
2021 Events
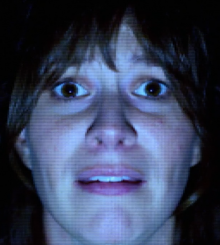
True Eye - Cinema Event
Beginning October 1, 2021 On Demand
True Eye is a thriller which follows new-hire, Adrian Bridges, through his first day at a global AI-technology firm. Adrian’s policy orientation and security training quickly spin into suspense and intrigue as his personal AI device, Guide, starts asking him to do unethical and even dangerous things with sensitive data. His adventure offers a glimpse into proper operational security, how technology affects people and what we can do about it.
Feature (Full length video : 17:54 minutes)
Zero Trust Networking - with Jon Green, VP and Chief Security Technologist at Aruba, a Hewlett Packard Enterprise company
October 4, 2021 Noon - 1 PM
(Hosted by UC Santa Barbara)
Jon Green is the VP and Chief Security Technologist at Aruba, a Hewlett Packard Enterprise company describes himelf as a Cybersecurity guy with a technical background in routing, switching, wireless, authentication, PKI, firewalls, and crypto. "I have a bunch of industry certifications, which proves that I'm good at taking multiple-choice tests. I fly airplanes, don't do CrossFit, and am a lousy but aspiring guitar and banjo player."
Best Practices Learned from Combating Hackers During the Attack - with James Christiansen, CSO VP, Cloud Security Transformation, Netskope, and James Robinson, Deputy CISO, Netskope
October 5, 2021 10 AM - 11 AM
(Hosted by UC San Francisco)

We all understand the essential need for a cyber-incident response plan. But what are the consequences, when, in the middle of a cyber-attack, your mitigation efforts are not going as planned? This session will focus on actual case scenarios where things did go wrong and the hacker was given the advantage! Best practices learned from combating hackers during the attack.
James Christiansen is Netskope’s vice president of cloud security transformation and leader of the Global Chief Strategy Office. He is focused on enhancing Netskope’s global clients understand the challenges and solutions of cloud deployments by helping drive thought leadership in cloud security transformation. James brings extensive expertise as a global leader in information security. Prior to joining Netskope, he was vice president CISO at Teradata where he led the global security, physical, and information security teams. Previously, James was vice president of information risk management at Optiv, chief information risk officer for Evantix, and CISO at Experian Americas, General Motors, and Visa International.
James Robinson is Netscope's Deputy CISO. He is a seasoned professional with nearly 20 years of experience in security engineering, architecture and strategy. He develops and delivers a comprehensive suite of strategic services and solutions that help executives change their security strategies through innovation.Before his time at Netskope, Robinson was the VP third-party risk management at Optiv, where he worked as a core contributor around strategic internal initiatives including threat management, risk management, third-party risk management, vulnerability management and data program protection. Prior to Optiv, he was the security architecture and strategy officer for Websense. He also previously served as product security officer for Emerson Network Power, a division of Emerson Electric Company, where he built the company’s first product security organization, including program and reference models, which were later adopted by Emerson Electric’s CTO office.He has held positions of increasing responsibilities with other Fortune 500 companies such as Anheuser-Busch and State Farm insurance where he ran one of the most successful penetration testing engagements in the company’s history.Throughout his career, Robinson has helped companies plan, build and run security programs, and he has developed solutions for network architecture and application security, penetration testing, incident response, security and risk assessment, forensics and investigations and product security. He attended Webster University where he studied business and management and holds a number of technical certifications.
Using Zoom Security & Awesome New Features - with Vanessa Moriarty
October 6, 2021 Noon - 1 PM
(Hosted by UC Santa Barbara)

It has been another year of utilizing Zoom as our primary communication tool across the UC System. Vanessa Moriarity from Zoom will discuss Zoom’s new advanced security features and best practices and how to effectively use them to keep your meetings safe and secure. In addition, she will explore some awesome new features and how to incorporate them successfully into your Zoom sessions.
LIVE from Las Vegas, The Mentalist
October 6, 2021 3 PM - 4 PM
(Hosted by UC Office of the President)

Join us for this family-friendly LIVE, interactive event! The Mentalist, straight from Las Vegas, will perform astounding feats such as telepathy, illusions, mind reading, and even magic for the younger attendees. Embedded in these feats will be security awareness lessons around social engineering and data privacy. Invite your children to join you for this educational and action-packed performance!
Ransomware - with Chad Spensky, Founder & CEO - Allthenticate
October 7, 2021 10 AM - 11 AM
(Hosted by UC Santa Barbara)
Chad is a computer security researcher, entrepreneur, and educator who is passionate about using technology to make people’s lives easier and their digital systems more secure. Chad has more than 10 years of research experience and is a lifetime hacker. Formerly, he was a member of the technical research staff at MIT Lincoln Laboratory and has since continued to help them solve some of the Department of Defense's toughest cyber-security problems. He received his Ph.D. from the University of California, Santa Barbara in 2020 (thesis title: Securing and Analyzing Embedded Systems). He also possesses a M.S. in computer security from the University of North Carolina at Chapel Hill, as well as a B.S. in mathematics, a B.S. in computer science, and a minor in economics from the University of Pittsburgh. As a hacker and capture the flag player himself, he is well aware of how attackers think and strongly believes that it takes a great offense to build a solid defense. He plans to use his experience and expertise to create a world that is more secure and more pleasant to interact with.
The Danny Ocean of Social Engineers - with Shelby Dacko, Human Risk Analyst and Social Engineer
October 11, 2021 10 AM - 11 AM
(Hosted by UC Office of the President)
Have you ever wondered what the day-to-day life of a social engineer looks like? This talk gives you the insider view and a guide to dealing with impostor syndrome. Shelby will discuss:
Perceptions of social engineers versus reality
Dealing with the impostor syndrome
Finding your strength
Branching out
Shelby Dacko is a Human Risk Analyst with Social‐Engineer, LLC. Shelby’s specialties include vishing, OSINT work, and educational material production. She also enjoys public speaking and teaching. Shelby’s most recent panel was at DerbyCon: Finish Line, entitled “Vishing: Real Vs. Competition, what’s the difference?”, where she spoke alongside Alethe Denis, Whitney Maxwell, Chris Silvers, and Colin Hadnagy.
In addition to her work at Social-Engineer, Shelby also volunteers for the Innocent Lives Foundation. The Innocent Lives Foundation is a nonprofit organization that unmasks anonymous online child predators to help bring them to justice.
Shelby is a certified Social Engineering Pentest Professional (SEPP), has her bachelor’s degree in Teaching English to Speakers of Other Languages (TESOL), and is a trained American Sign Language (ASL) Interpreter.
In her free time, Shelby also enjoys studying psychology as well as painting.
Shelby defines social engineering as the act of using what you know about human behaviors to bring about your desired outcome.
Social Engineering - with Chad Spensky, Founder & CEO - Allthenticate
October 12, 2021 Noon - 1 PM
(Hosted by UC Santa Barbara)
Chad is a computer security researcher, entrepreneur, and educator who is passionate about using technology to make people’s lives easier and their digital systems more secure. Chad has more than 10 years of research experience and is a lifetime hacker. Formerly, he was a member of the technical research staff at MIT Lincoln Laboratory and has since continued to help them solve some of the Department of Defense's toughest cyber-security problems. He received his Ph.D. from the University of California, Santa Barbara in 2020 (thesis title: Securing and Analyzing Embedded Systems). He also possesses a M.S. in computer security from the University of North Carolina at Chapel Hill, as well as a B.S. in mathematics, a B.S. in computer science, and a minor in economics from the University of Pittsburgh. As a hacker and capture the flag player himself, he is well aware of how attackers think and strongly believes that it takes a great offense to build a solid defense. He plans to use his experience and expertise to create a world that is more secure and more pleasant to interact with.
UC Cyber Security Summit
October 13, 2021 9 AM - 4 PM

The 12th Biannual Cyber Security Summit will be held online on October 13th. We are excited about sharing our collective expertise in order to better safeguard UC’s mission of teaching, research, and public service.
Registration Required
FireEye Presents - Safety for Families
October 14, 2021 Noon - 1 PM
(Hosted by UC Office of the President)


Ric Messler, Principal Security Consultant, FireEye Mandiant
Ric Messier is a consultant, author, and educator who holds CCSP, GCIH, GSEC, CEH, and CISSP certifications, and has published several books on information security and digital forensics. With decades of experience in information technology and information security, Ric has held the varied roles of programmer, system administrator, network engineer, security engineering manager, VoIP engineer, consultant, and professor.
Choose Your Own Cybersecurity Adventure: How to get started and succeed in the InfoSec field with Nathan Wenzler, Chief Security Strategist at Tenable
October 18, 2021 Noon - 1PM
(Hosted by UC Berkeley)
It's no secret that technology is evolving faster and faster each day. Which means the types of skills and the needs of organizations to protect and secure those technologies is changing just as quickly. Trying to get started in the Information Security or Cybersecurity fields can be difficult, at best, with the ever-changing curriculums and often unreasonable levels of skill being asked for by many hiring managers. For both students and educators, it can be difficult to know what the most relevant courses are, what topics should be focused on and what additional skills will help position the next generation of security practitioners for success. And this leads to the questions: What area of cybersecurity should I specialize in? How do I demonstrate skill and experience when I'm first interviewing? How do we better prepare students to be successful in their careers? Are there some skills and knowledge that are more in demand than others?
In this discussion, Nathan Wenzler, Chief Security Strategist at Tenable, the creators of Nessus and the leaders in Risk-Based Vulnerability Management, will share what he's seen work for both educators and students over a 25 year career of mentoring new practitioners and leaders in the cybersecurity field as well as what trends are being seen in the industry for what skills and topics both students and educators should include in their programs to remain relevant for the future.
Nathan has been designing, implementing, and managing technical and non-technical solutions for IT and information security organizations since 1997. He has helped government agencies and Fortune 1000 companies build new information security programs from scratch, as well as improve and broaden existing programs with a focus on process, workflow, risk management, and the personnel side of a successful security effort. Nathan brings his expertise on security program development and implementation in both the public and private sector to administrators, auditors, managers, C-Suite executives, and security professionals across a wide variety of organizations and companies around the globe.
Nathan is frequently quoted in publications such as USA Today, Forbes, The Washington Post, TheStreet.com, Infosecurity Magazine, Dark Reading, SC Magazine, and contributes regularly to his own column on CSO Online, The Layer 8 Debate. He is also a frequent presenter on BrightTalk and at a number of leading conferences worldwide.
The State of Authentication with Chad Spensky, Founder & CEO - Allthenticate
October 19, 2021 Noon - 1 PM
(Hosted by UC Santa Barbara)
Chad is a computer security researcher, entrepreneur, and educator who is passionate about using technology to make people’s lives easier and their digital systems more secure. Chad has more than 10 years of research experience and is a lifetime hacker. Formerly, he was a member of the technical research staff at MIT Lincoln Laboratory and has since continued to help them solve some of the Department of Defense's toughest cyber-security problems. He received his Ph.D. from the University of California, Santa Barbara in 2020 (thesis title: Securing and Analyzing Embedded Systems). He also possesses a M.S. in computer security from the University of North Carolina at Chapel Hill, as well as a B.S. in mathematics, a B.S. in computer science, and a minor in economics from the University of Pittsburgh. As a hacker and capture the flag player himself, he is well aware of how attackers think and strongly believes that it takes a great offense to build a solid defense. He plans to use his experience and expertise to create a world that is more secure and more pleasant to interact with.
Diversity Equity and Inclusion Series: Women In Leadership In Technology Panel Discussion with Charron Andrus, Sian Shumway, and Jane Wong - Moderated by Reema Moussa
October 20, 2021 Noon - 1 PM
(Hosted by UC Office of the President)
Charron Andrus is Associate CISO at UC Berkeley. Charron focuses as an advocate for a diverse, inclusive, and equitable faculty, staff, and student body and her passion is engaging in and creating meaningful relationships with community partners. She is the co-founder of the Black Leadership Alliance Council at the University of California (BLAC@UC) and has served on several campus and systemwide committees including serving as a Delegate to the UC Council of Staff Assemblies for two years as well as being an Officer of the Council. Charron founded Andrus Consulting in February 2021 to provide career guidance and advice to Black women and other diverse groups. In her spare time, Charron enjoys writing and has published a book of poems entitled Words That Occur in the Absence of Love.
Sian Shumway is Director of UCSF IT Customer Service providing leadership for all aspects of IT Customer Service including, IT Service Desk, Field Services, Desktop Engineering, Unified Communications and IT Service Management. Sian ensures exceptional customer satisfaction through strategic and operational leadership in developing and implementing best practice IT customer service solutions enterprise-wide at UCSF.
Jane Wong is Vice President and Associate CIO for enterprise applications in the UCSF information technology department. She joined UCSF from the commercial sector, and she has brought with her the culture of innovation and creativity. Jane continues to serve as WIT@UCSF's executive sponsor and mentor.
Reema Moussa is a law student at the University of Southern California Gould School of Law. She graduated from UCSB with undergraduate degrees in Communication and Global & International Studies and a Masters in Technology Management, where she worked on the UCSB Information Security Team as the Cybersecurity Awareness Coordinator and founded the UCSB Chapter of Women in Cybersecurity (WiCyS). As a passionate advocate of diversity, equity, and inclusion in the workplace, Reema has worked to empower women and girls to pursue careers in tech and cybersecurity through her role as leader of WiCyS UCSB and as the Girls in ICT Coordinator for ITU in 2021, before relocating to Los Angeles to begin law school and jumpstart a career in data privacy and cyberlaw.
FireEye Mandiant Presents - Ransomware: What Everyone Needs to Know
October 21, 2021 Noon - 1 PM
(Hosted by UC Office of the President)

Jason Wright, Senior Manager at Mandiant Consulting
Jason is a seasoned cybersecurity professional with 20 years front line experience in responding to ransomware incidents which provides incredible insights in not only how to respond to incidents, but also help organizations protect against ransomware situations. Join Jason as he shares his front line experience on what we can all do as individuals in our organization and in our personal lives to keep vigilant in protecting our important data.
Amusing Hacker Stories - with Chad Spensky, Founder & CEO of Allthenticate
October 26, 2021 Noon - 1 PM
(Hosted by UC Santa Barbara)


“Hackers” have become emblazoned in our society. They dominate news headlines, are featured in prominent Hollywood movies, and have become larger than life -- instilling fear in IT professionals and awe in many young computer scientists. Who are these people, what does it mean “hack” something, and what the heck is a binary? Surely, you have seen a news headline that talks about hackers stealing data, taking over cars, or disrupting power plants and thought to yourself, “how did they do that; is that even possible?”
In this talk, my goal is to convince you that “hacking” isn't that hard, and try to tease apart fact from fiction with respect to hackers. I will highlight some hacking techniques and show you how to “own” a computer. We will explore some of the technical limitations of our current computing systems and why they are exploitable. Finally, I will walk you through a simple example of binary exploitation, and how you can make a program do things it wasn't intended to do. At the end of this talk, you should be able to read news headlines with sufficient skepticism and, in some rare cases, considerable respect for the hacker’s skills.
Using Zoom Security Improvements & Cool New Features
October 27, 2021 Noon - 1 PM
(Hosted by UC Santa Barbara)
It has been another year of utilizing Zoom as our primary communication tool across the UC System. Vanessa Moriarity from Zoom will discuss Zoom’s new advanced security features and best practices and how to effectively use them to keep your meetings safe and secure. In addition, she will explore some awesome new features and how to incorporate them successfully into your Zoom sessions.
FBI Presentation: Cyber Threatscape
October 26, 2021 11 AM - Noon
(Hosted by UC Irvine)

Cyber Threatscape: Understanding what the cyber threats are to UC Faculty and Students. The FBI will share their perspectives on the cyber threat landscape, and will provide tips to protect themselves from these threats.
Supervisory Special Agent (SSA) Michael Sohn is currently leading a squad at the FBI Los Angeles Field Division that is responsible for investigating computer and high-technology crimes. His investigative experience includes cyber terrorism, nation-state and criminal cyber intrusion matters. Prior to his employment with the FBI, he worked as a Cyber Counterintelligence Officer for the Department of the Army, a Counter Terrorism officer for the Defense Intelligence Agency, a consultant at Booz Allen Hamilton and a U.S. Army Officer. Mr. Sohn received a Bachelor of Science in Computer Science from the United States Military Academy, West Point and a Master of Science in Computer Information Systems from Boston University, Boston.