This content is viewable by Everyone
Jan 2026: NEW Cl0p EXTORTION THREAT
Threat Alert: NEW Cl0p EXTORTION THREAT
- The Cl0p threat actor group routinely uses extortion-style messages to extract funds, typically in the form of cryptocurrency, from recipients.
- The messages can be both fictitious and reflect real-world events, complicating organizational response.
How is it used in the wild?
- The Cl0p group has infamously engaged in the exploitation of new or zero-day vulnerabilities to exfiltrate sensitive data, then extorted victims to prevent their disclosure.
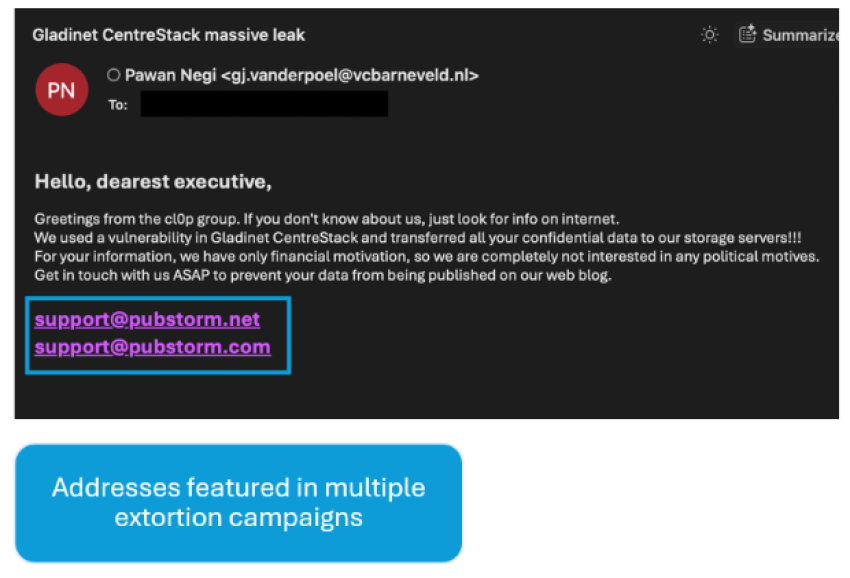
- This campaign claims to originate from Cl0p, purporting to have exploited the organization Gladinet’s CentreStack software.
- Messages threaten to post stolen files on the group’s data leak site (DLS), directing recipients to contact them via support@pubstorm[.]com and support@pubstorm[.]net (likely actor-controlled addresses) to negotiate payment.
Key Action: Stay Alert!
- Follow proper payment processes.
- Report ANY suspicious emails via Phish Alarm.