See the Red Flags from The latest UCSF Phishing Campaign
Information you need to know
WHAT YOU SHOULD DO IF YOU RECEIVE A RANDOM EMAIL OR CALL THAT ASKS FOR YOUR PRIVATE INFORMATION:
- Within UCSF email, click on the Phish Alarm
 Button to report it.
Button to report it. - Do not reply to or click on the link in the message.
- If it's a phone message, hang up.
Instead, if you believe the sender or caller to be a legitimate organization, open a new internet browser session and type in the company’s correct web address yourself.
If you're concerned about your account, contact the organization mentioned in the email or call, using a telephone number you know to be genuine.
- Be wary of telephone numbers listed in emails.
Some scammers send an email or make a call that appears to be from a legitimate business and ask you to call a phone number to update your account or access a “refund.” Because they use Voice Over Internet Protocol (VOIP) technology, if you call back, the area code you call does not reflect where the scammers really are.
- Validate the caller or sender.
If you need to reach an organization you do business with, call the number on your financial statements, the back of your credit card, or other official document.
- Don’t provide other peoples' personal or financial information without an approved business purpose and their consent.
Various laws and regulations mandate the protection of personal and financial data. These laws require organizations to obtain consent and have a legitimate purpose for data processing and sharing.
- Validate websites.
If you initiate a transaction and want to provide your personal or financial information through an organization’s website, look for indicators that the site is secure, such as a lock icon on the browser’s status bar or a URL for a website that begins “https:” (the “s” stands for “secure”). Unfortunately, no indicator is foolproof; some phishers have forged security icons. Validate the URL for the site.
- Review credit card and bank account statements as soon as you receive them.
Check for unauthorized charges. If your statement is late by more than a couple of days, call your credit card company or bank to confirm your billing address and account balances.
- Be cautious about opening any attachment or downloading any files from emails you receive, regardless of who sent them.
These files can contain viruses or other software that can weaken your computer’s security.
- Be careful what information you publicize.
Attackers may be able to piece together information from a variety of sources. Avoid posting personal data in public forums.
- Use and maintain anti-virus software and a firewall.
Protect yourself against viruses and Trojan horses that may steal or modify the data on your own computer and leave you vulnerable. Make sure to keep your virus definitions up to date.
Additional important information
- If you believe you have received a phishing message, but have NOT clicked the link or opened the attachment, report it by clicking on the Phish Alarm
 button within your UCSF email.
button within your UCSF email. - If you DID click on a link and download software, turn off your computer and contact the IT Service Desk immediately.
- If you clicked on a link and provided your credentials, change your password immediately and contact the IT Service Desk.
UCSF IT Service Desk
MAIN: 415-514-4100
APeX: 415-514-APEX
Fast, Efficient Solutions
UCSF-wide Phishing Campaigns - Phish Indicators (Red Flags)
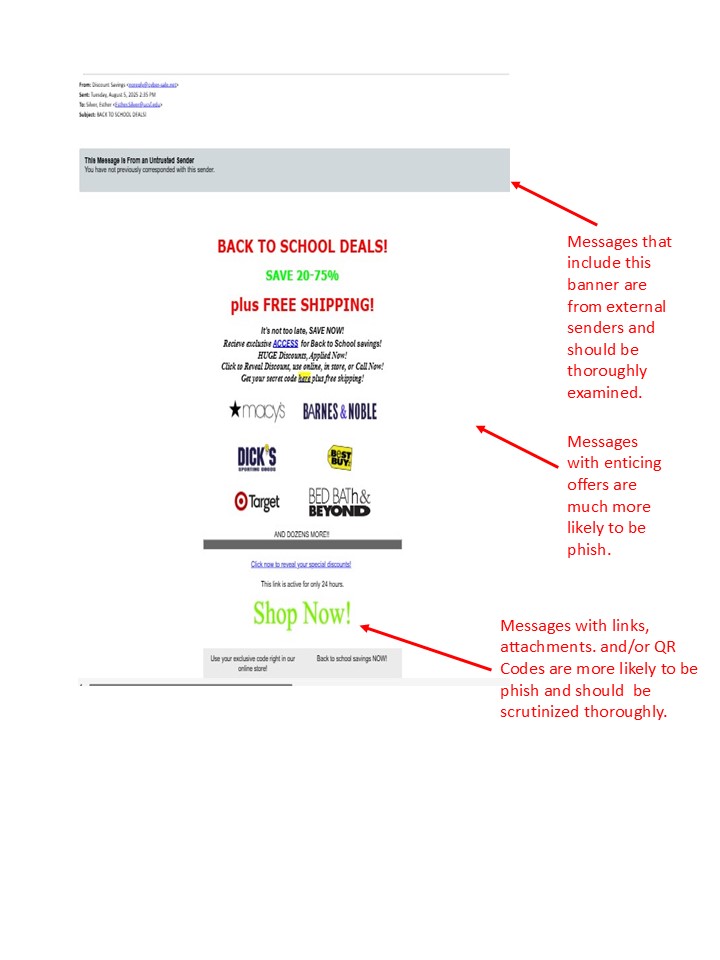
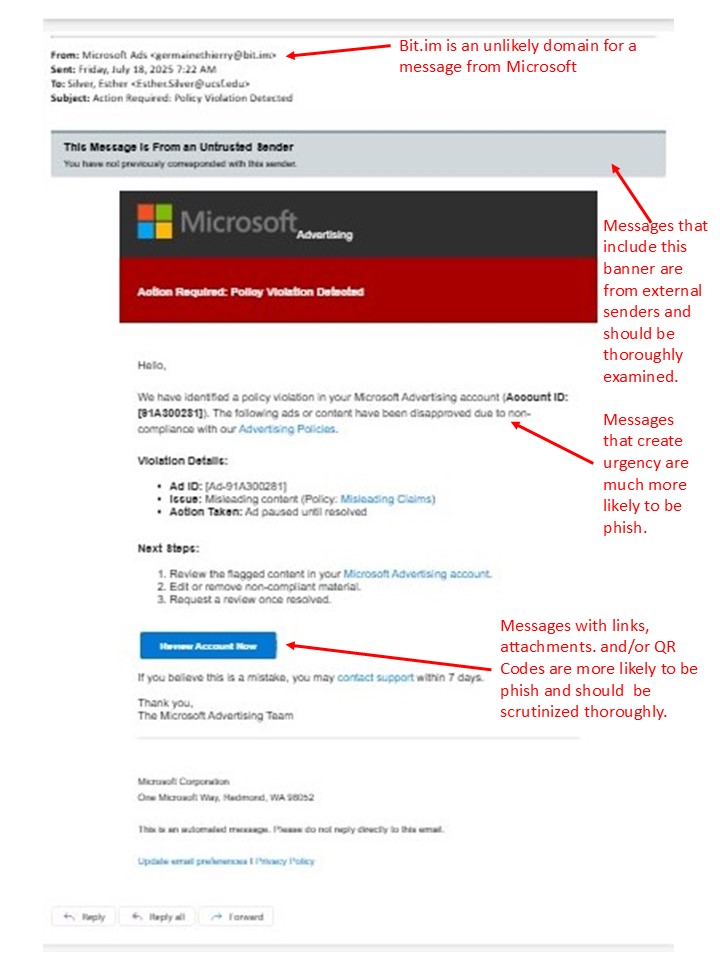
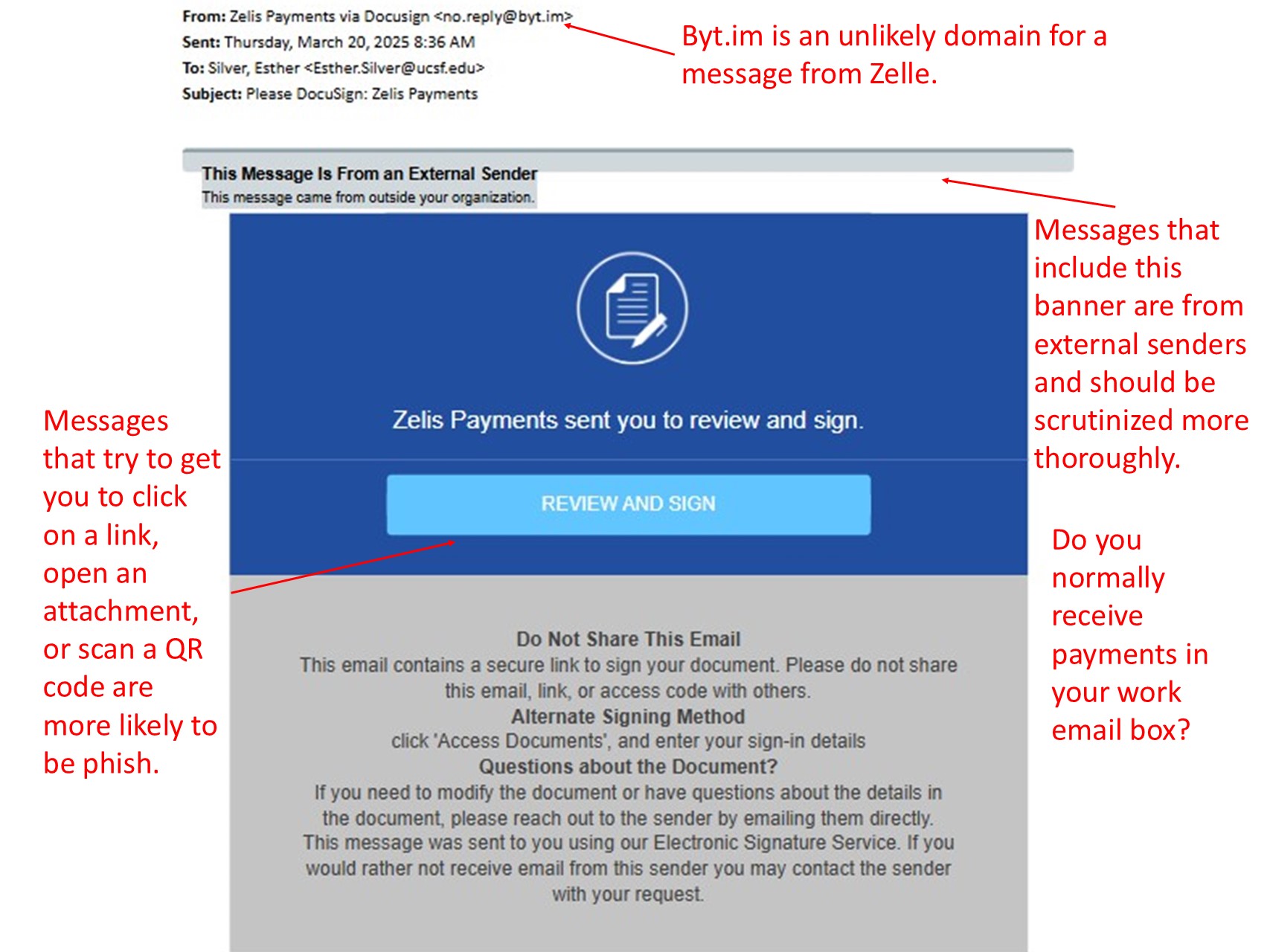
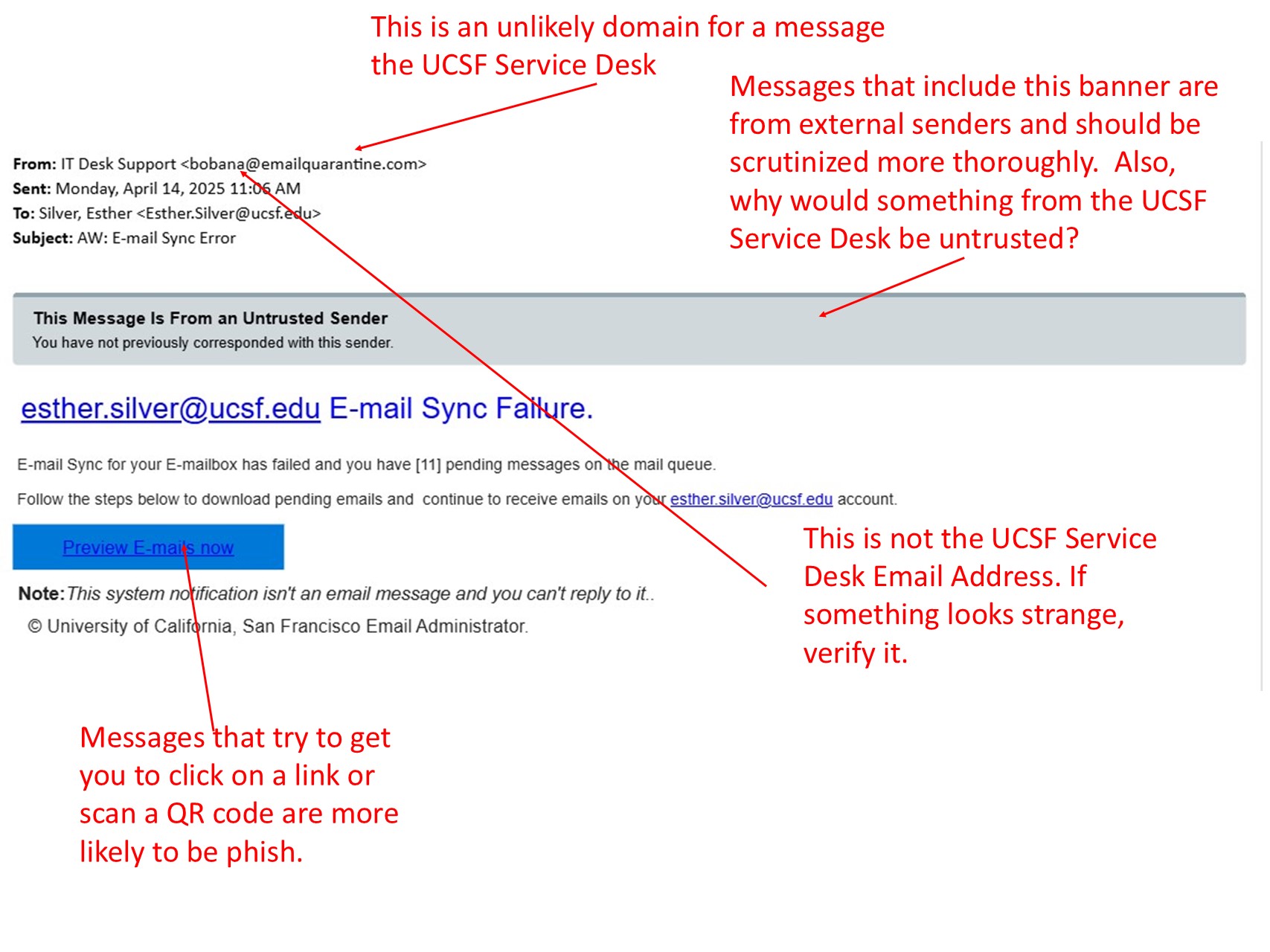
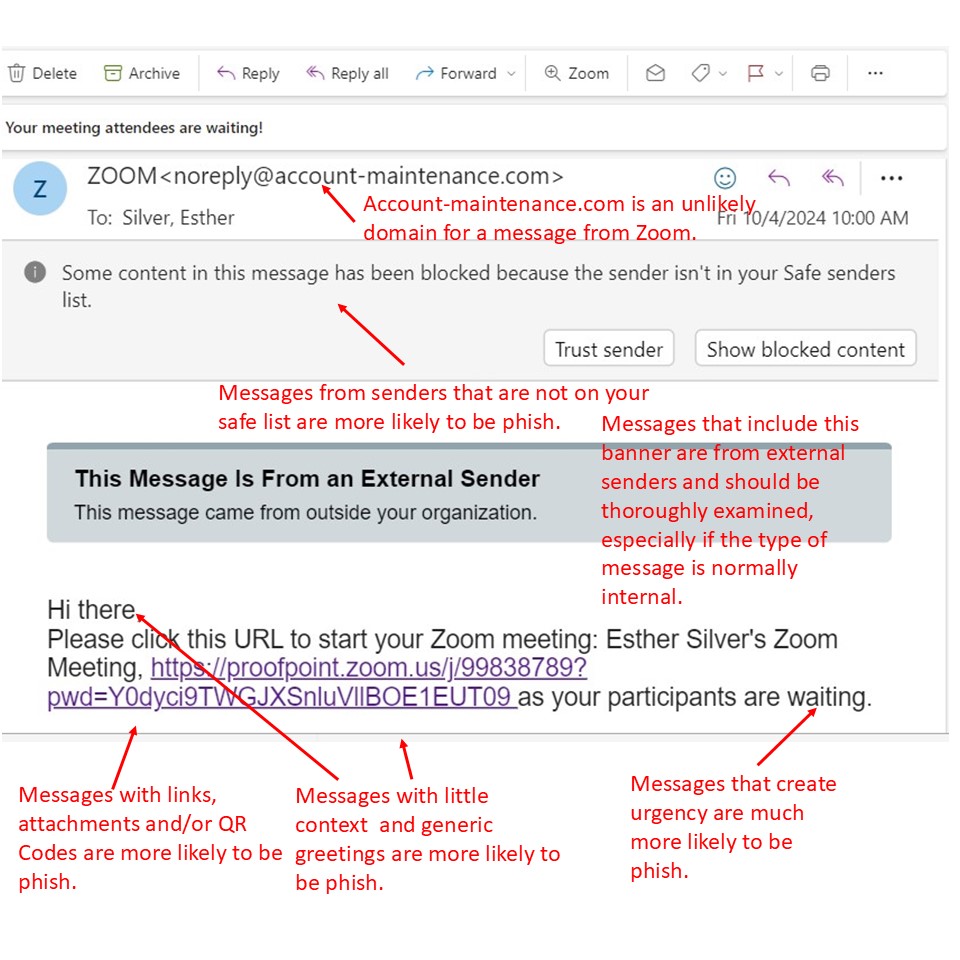
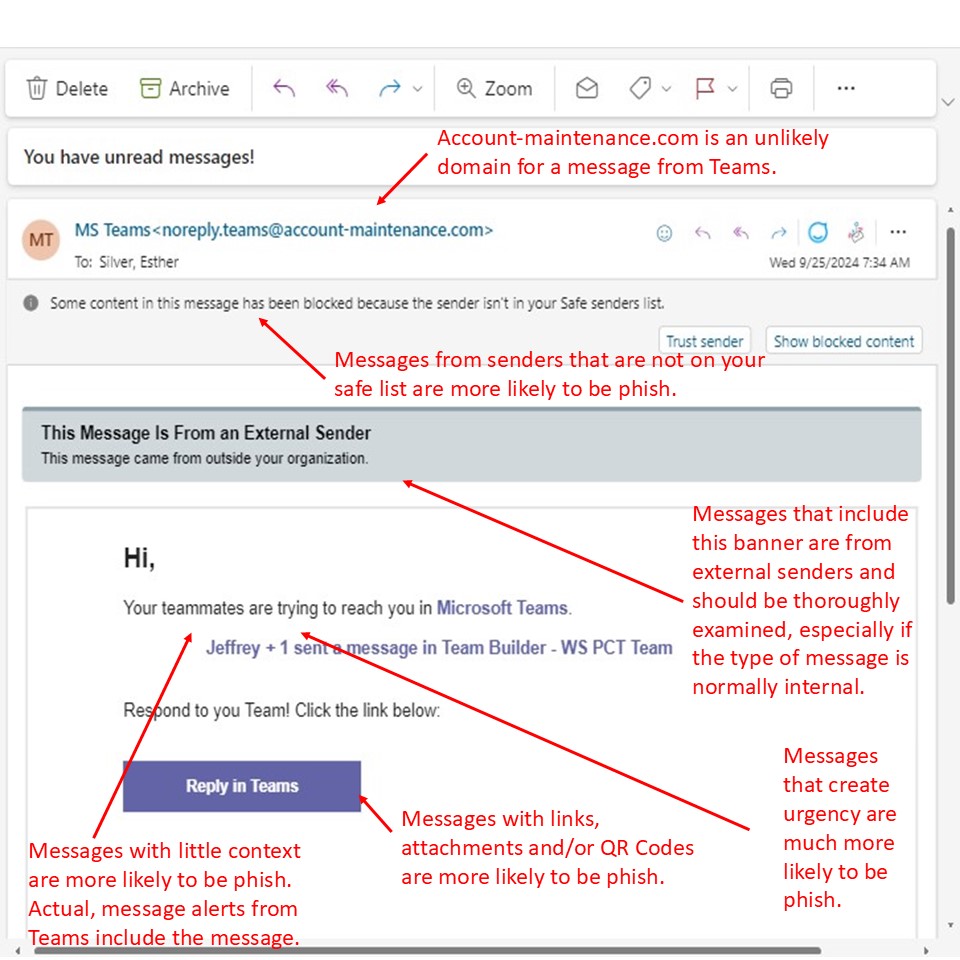
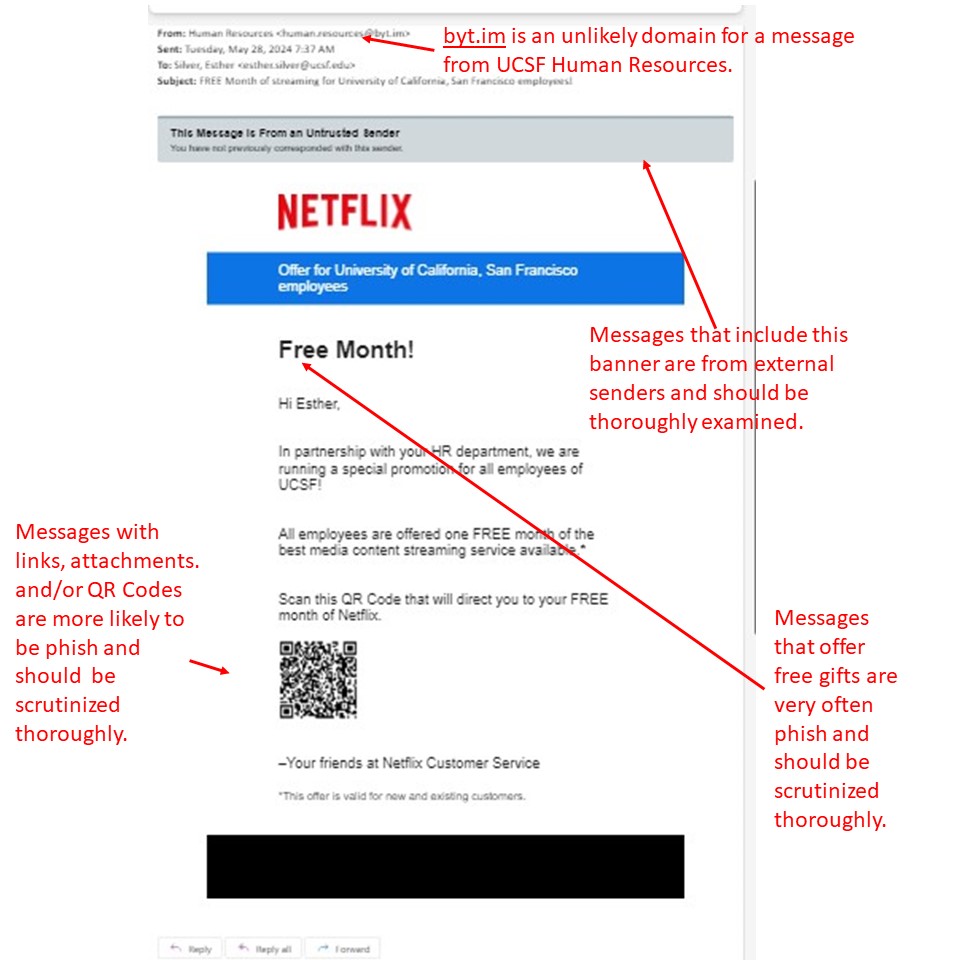
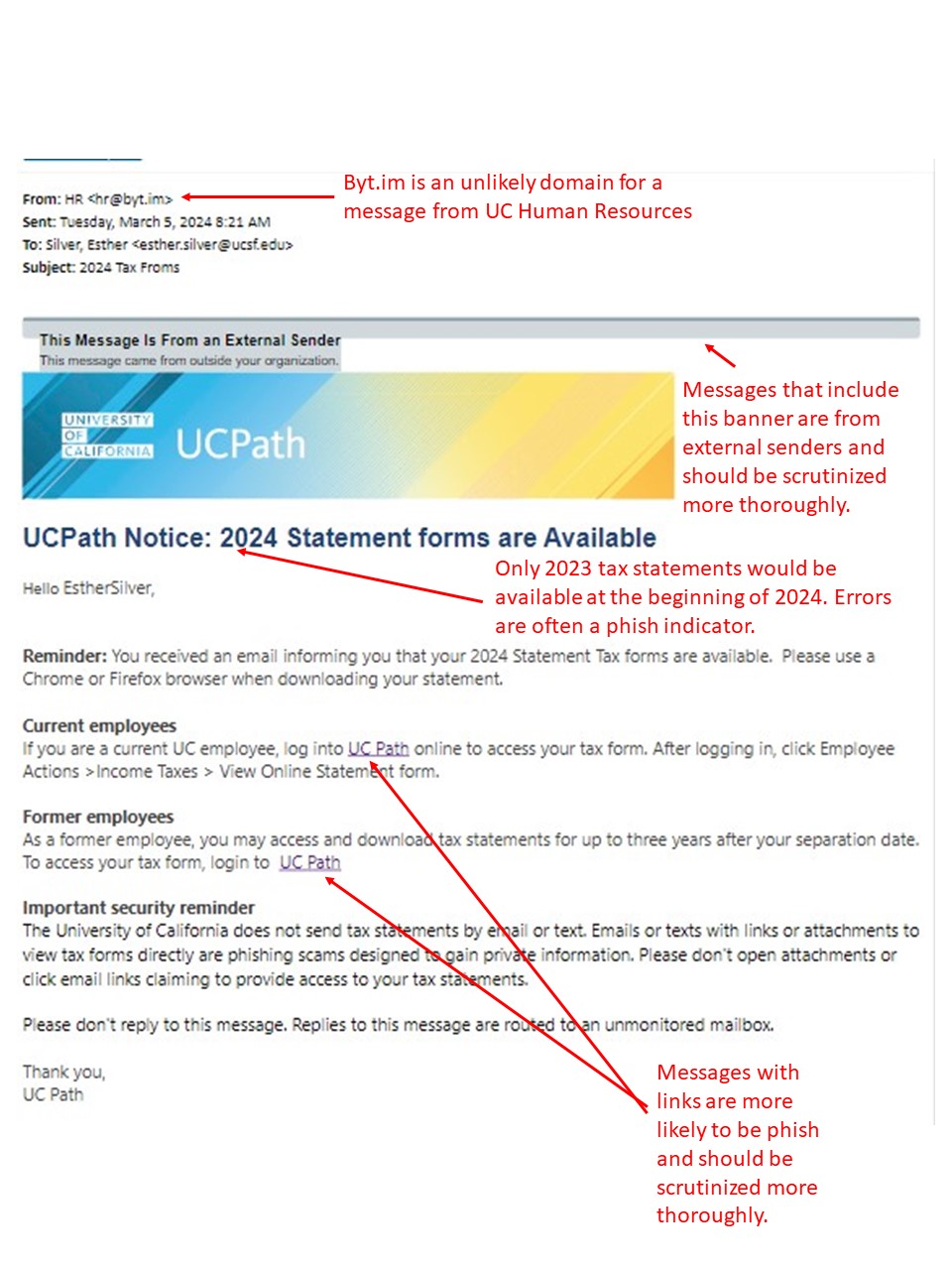
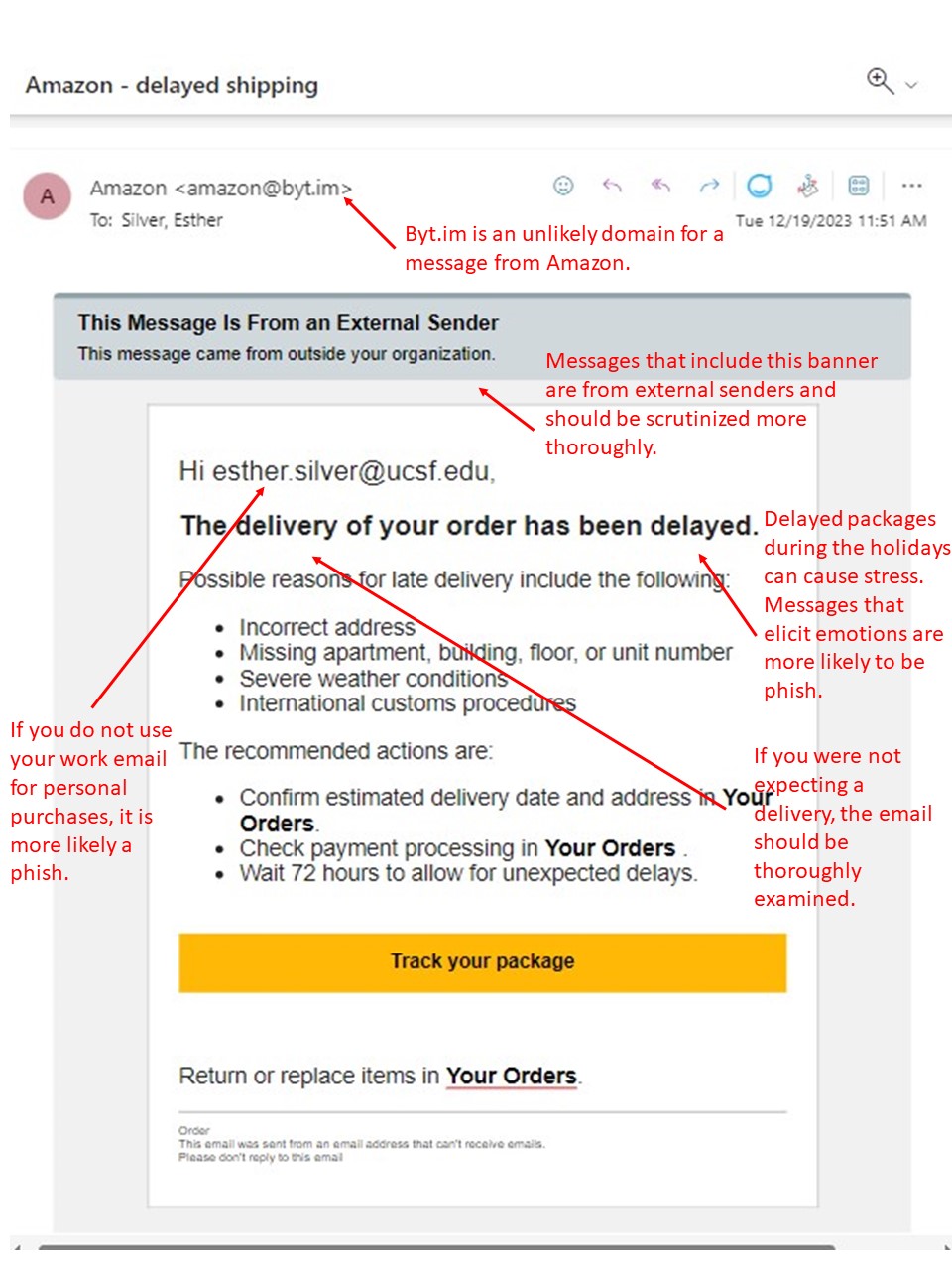
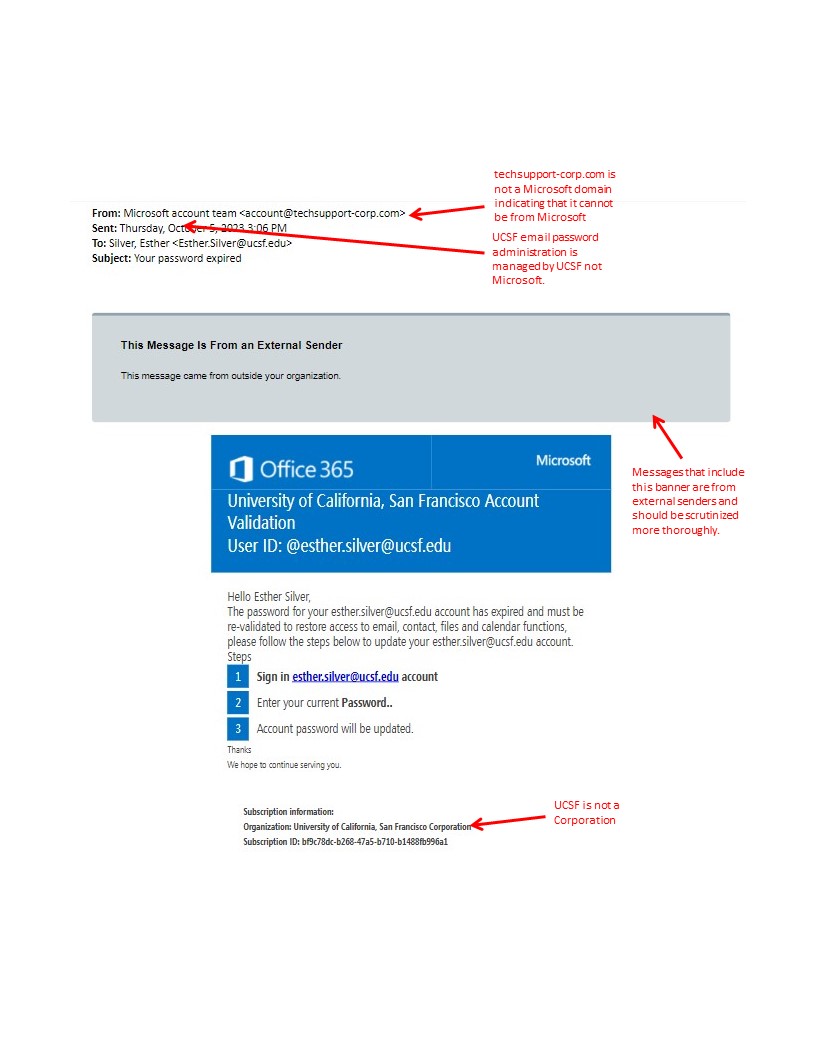
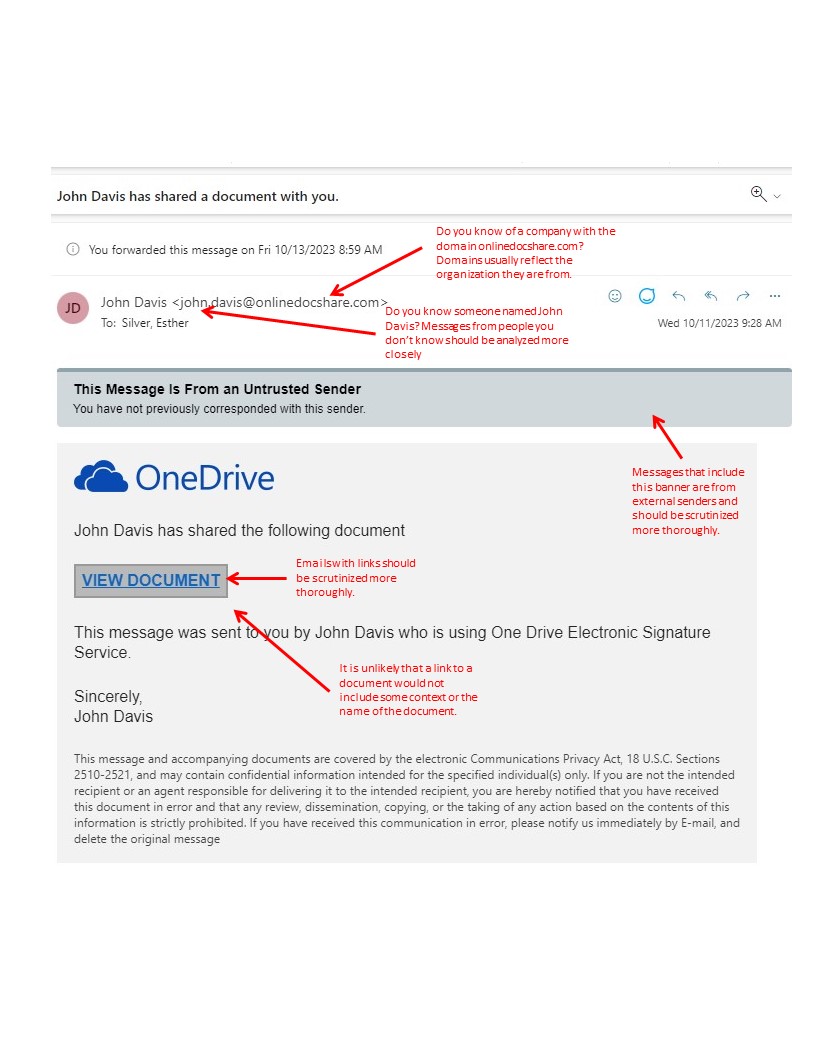
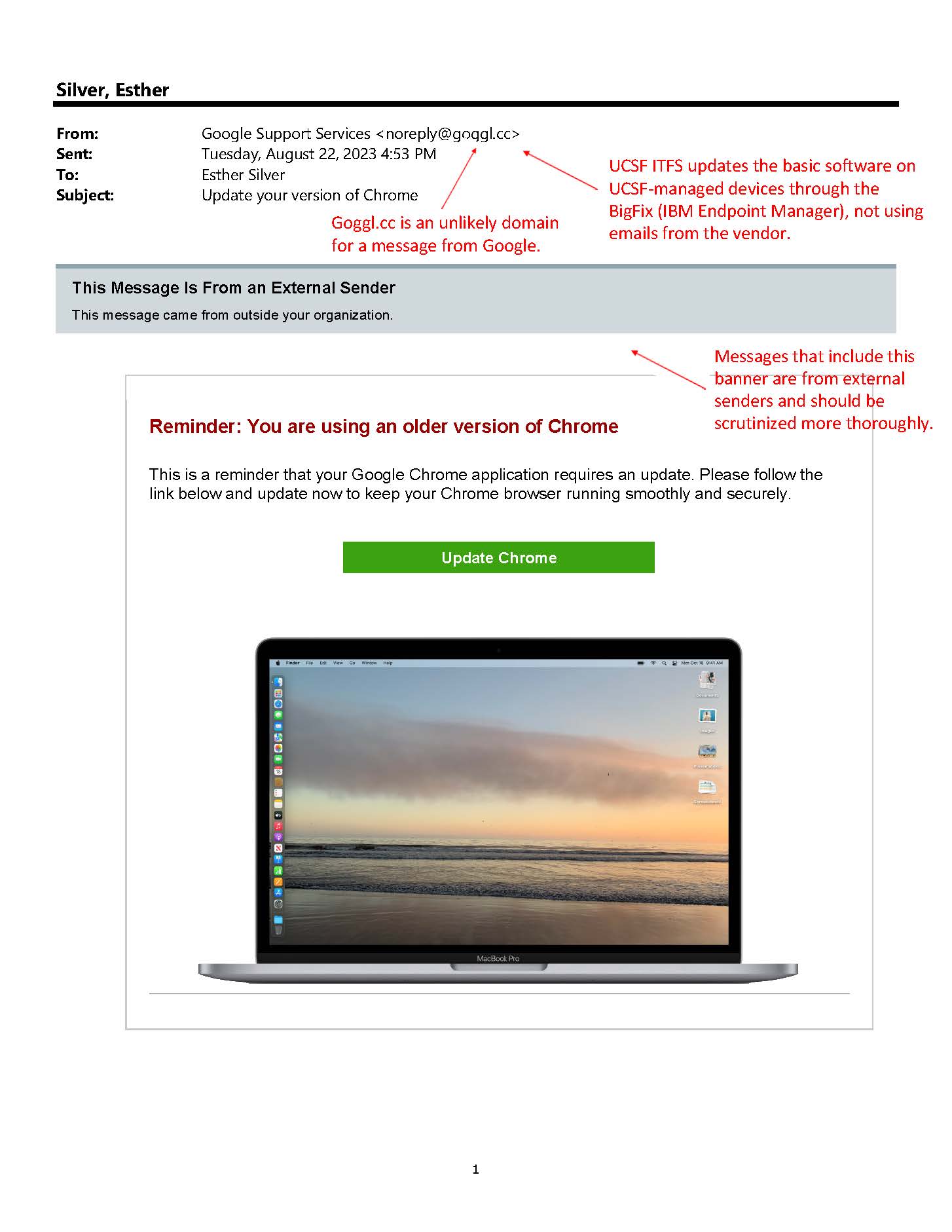
Below are pictures of the most recent mock phish. If something is at all strange, report it via Phish Alarm. It will analyze it and get back to you in minutes. Over-reporting is not an issue. It is always better to be safe than sorry!
March 2026 Tax Lure
March 2026 USPS Certified Mail Lure
October 2025 Uber Discount Lure
August 2025 Retest Back-to-School Bargains Lure
August 2025 Microsoft Error Lure
July 2025 Payroll Services Retest
June 2025 Zelis (Not Zelle) Message
June 2025 Mail Sync Retest Message
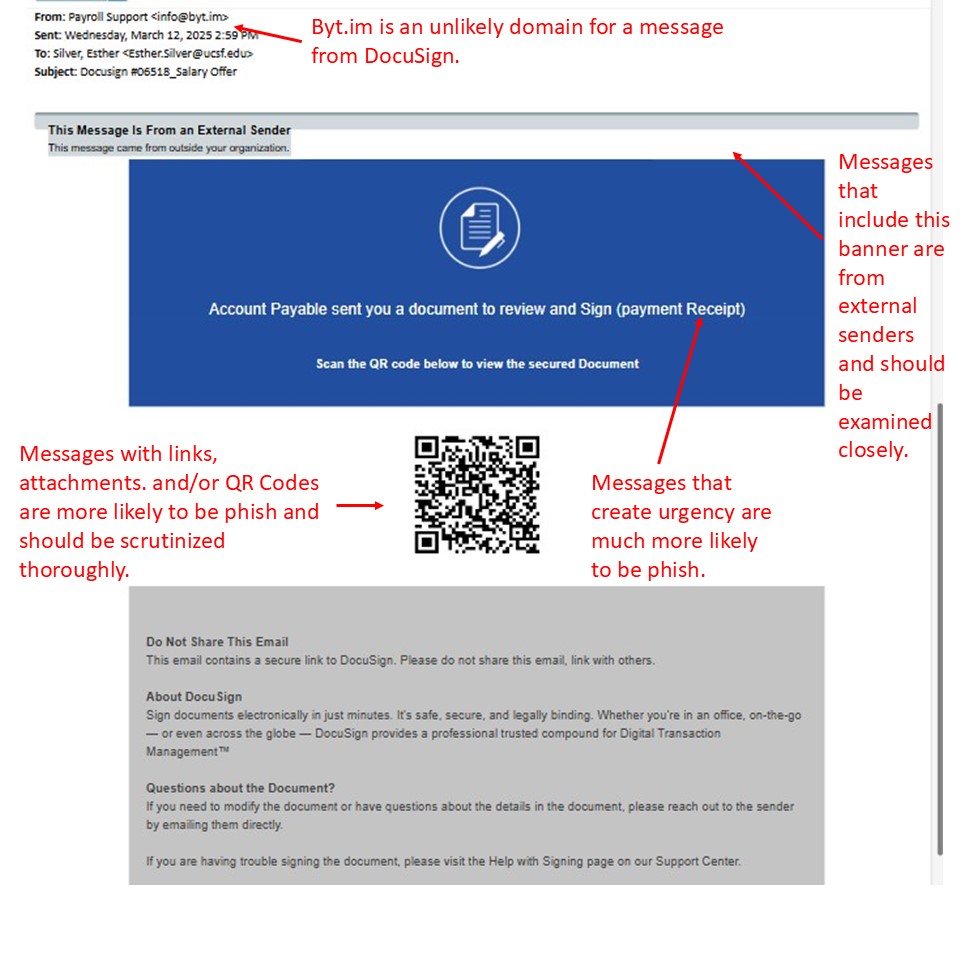
April 2025 DocuSign Message
March 2025 Zelis Retest Message
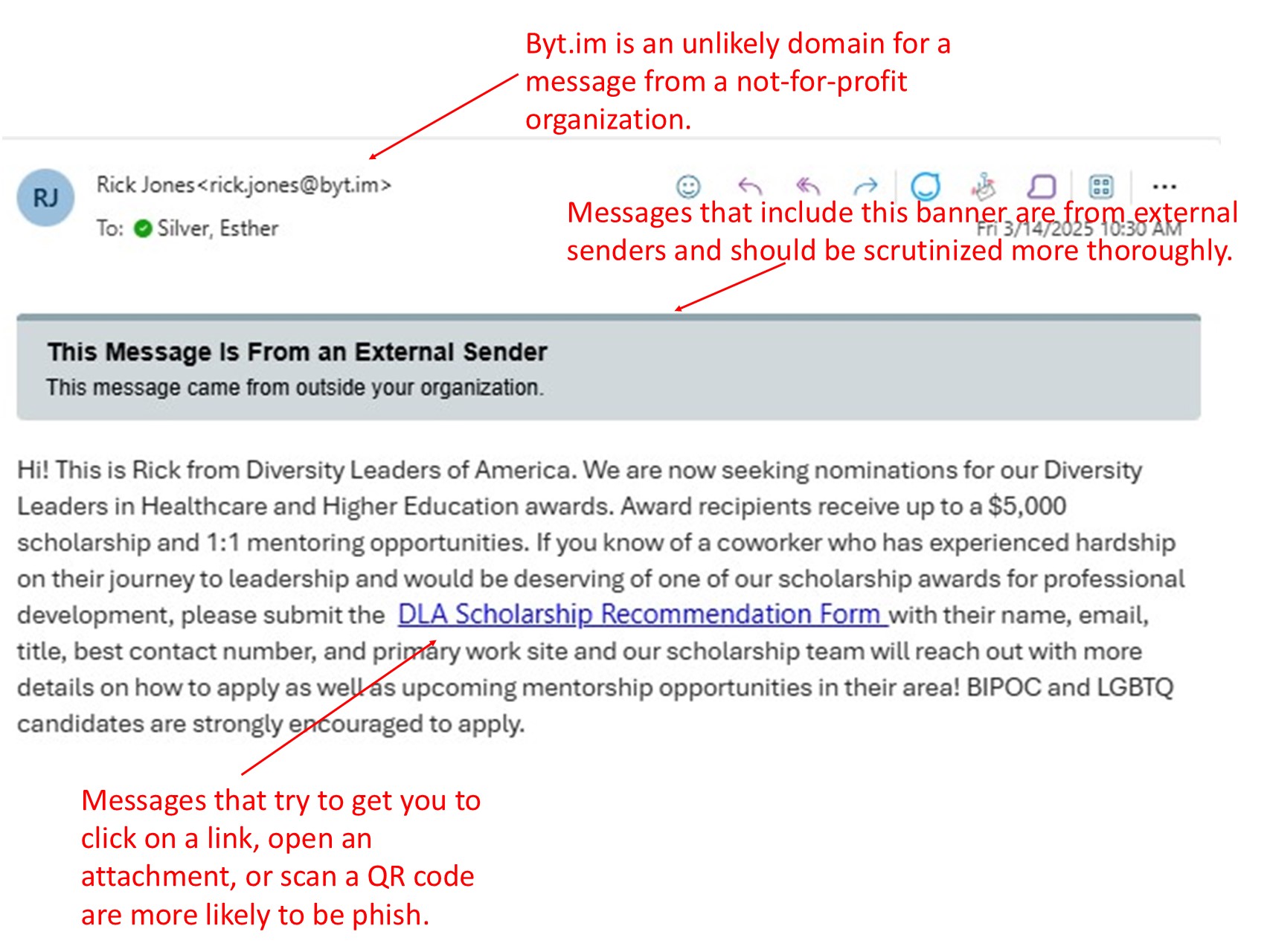
March 2025 Scholarship Message
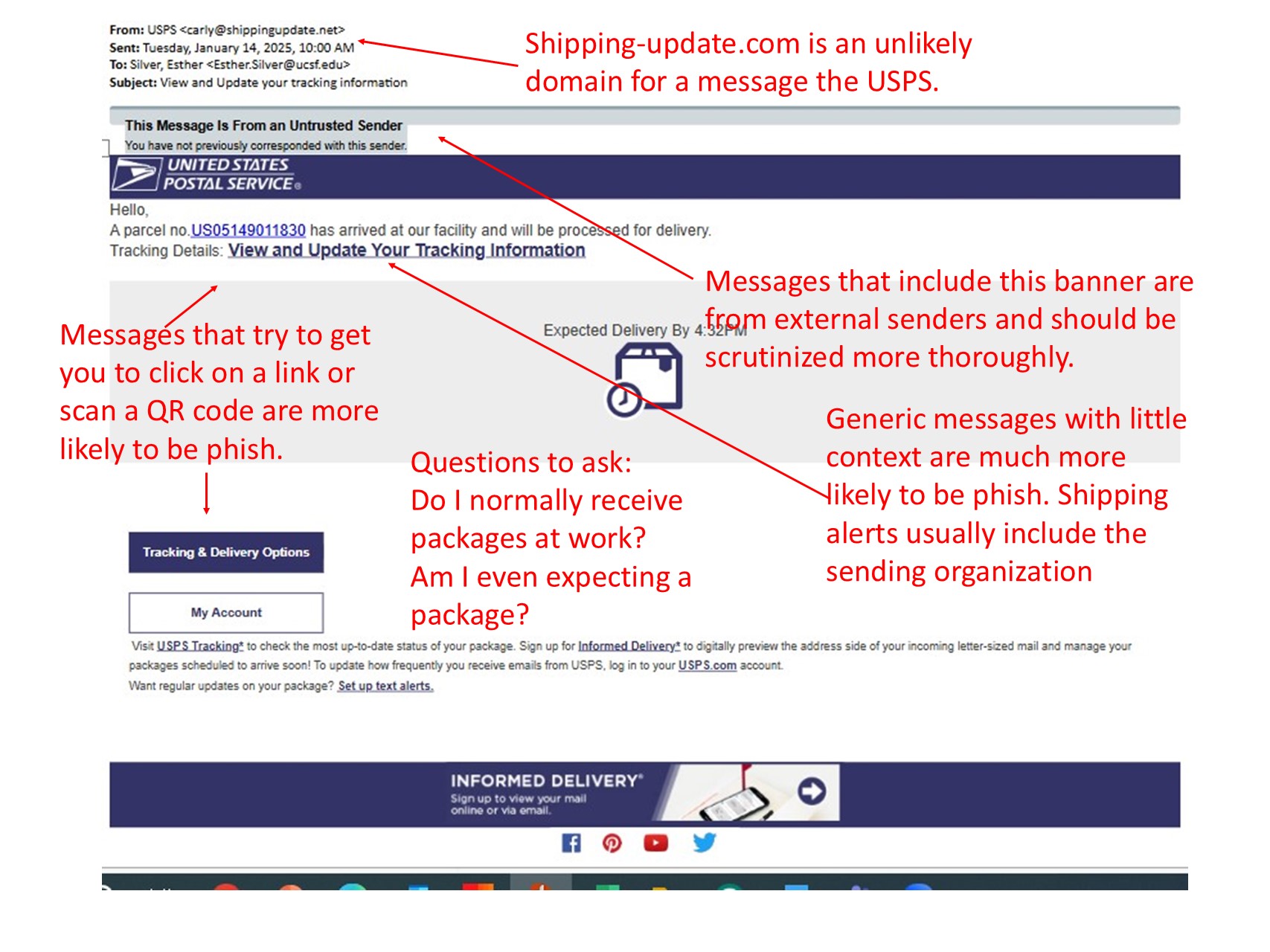
December 2024 USPS Message
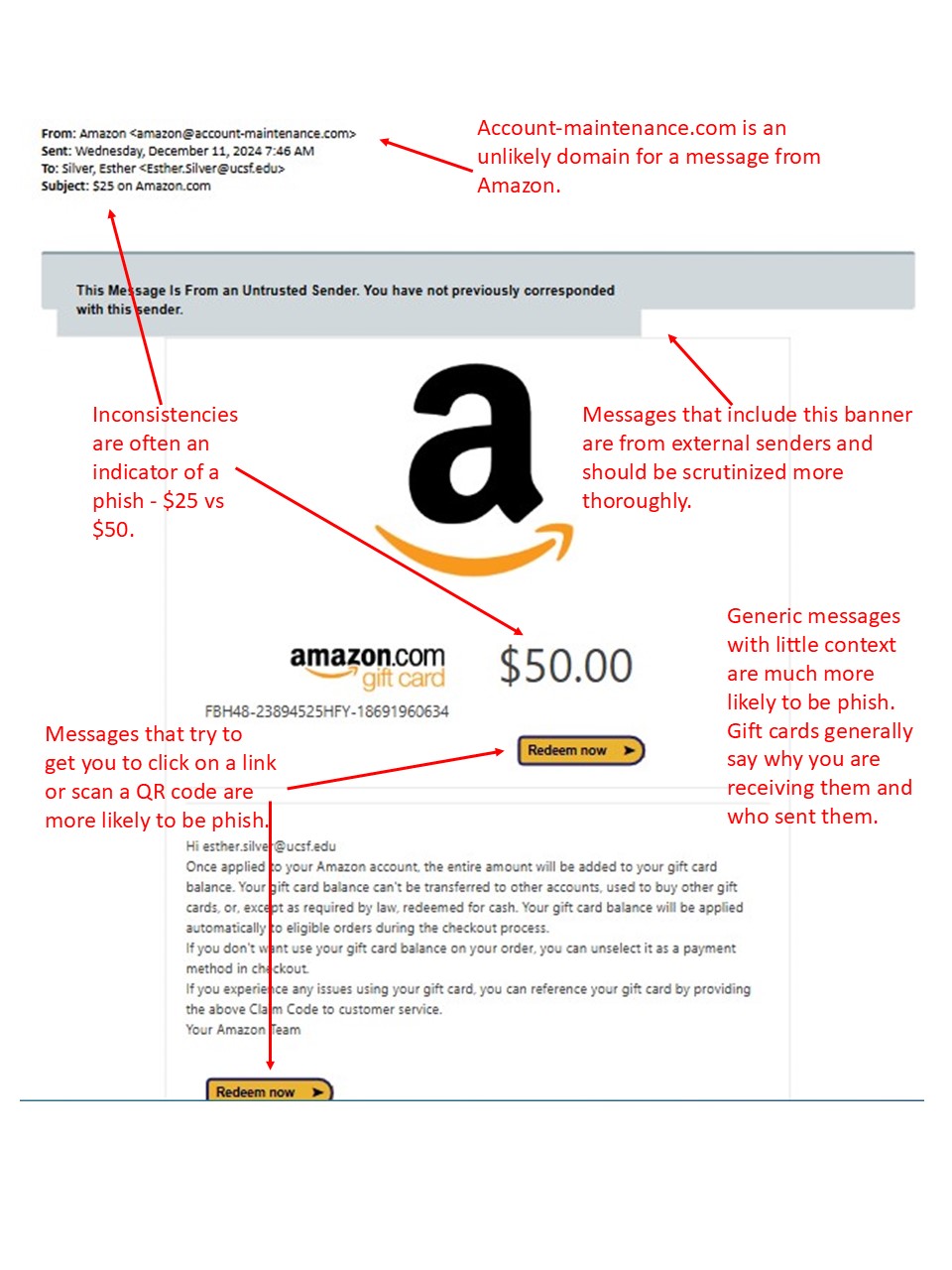
December 2024 Amazon Message
September 2024 Zoom Message
September 2024 Message in Teams
May 2024 Free Netflix Mock Phish to all of UCSF
April 2024 QR Phish to all of UCSF
March 2024 Phish to all of UCSF
December 2023 Retest Phish
December 2023 Phish to all of UCSF
October 2023 Mock Phish to all IT Employees
October 2023 Retest Mock Phish to IT Employees